OUR CAPABILITIES
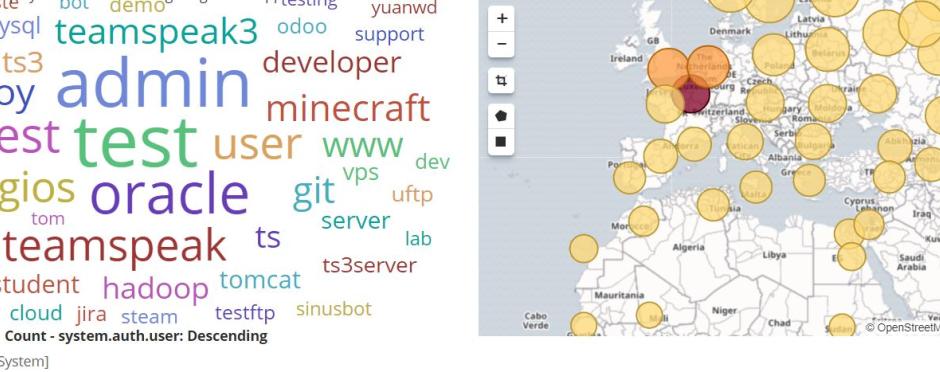
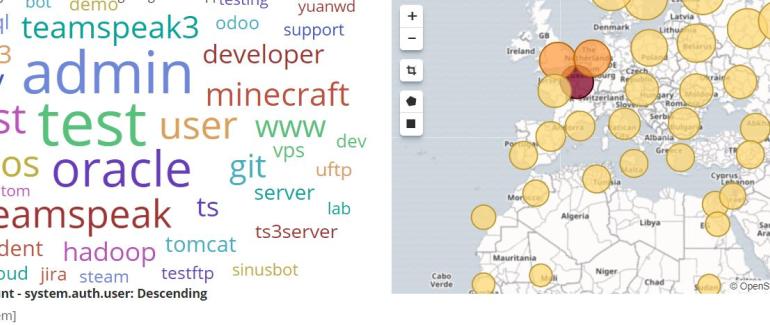
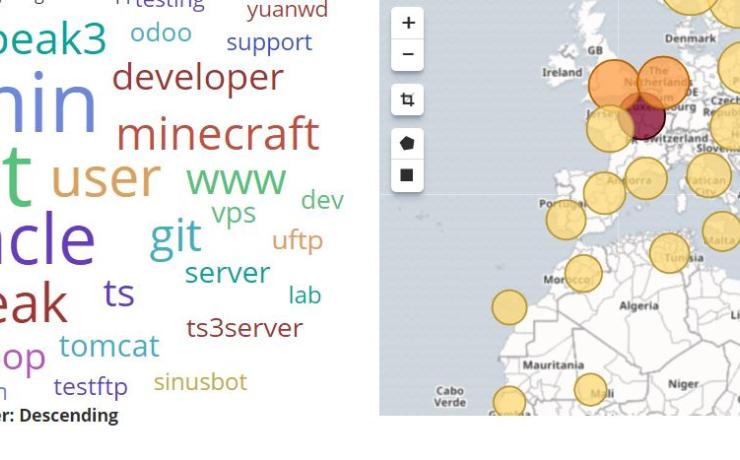
One of our recent projects was to install all of the components of the Elastic Stack, which includes Filebeat, a Beat used for forwarding and centralizing logs and files, and configuring them to gather and visualize system logs.
The Elastic Stack which used to be called the ELK Stack is a collection of open-source software produced by Elastic. Elastic Stack allows one to search, analyze, and visualize logs generated from any source in any format. This practice is often known as centralized logging. Centralized logging comes in very handy when one is attempting to identify problems with servers or applications, because it enables searching through all logs in a single place. Elastic Stack is also useful as it allows you to identify issues that related to multiple servers by correlating their logs during a specific time frame.
As part of the Elastic Stack project, the following components were installed:
- Elasticsearch: a distributed RESTful search engine which stores all of the collected data.
- Logstash: the data processing component of the Elastic Stack which sends incoming data to Elasticsearch.
- Kibana: a web interface for searching and visualizing logs.
- Beats: lightweight, single-purpose data shippers that can send data from hundreds or thousands of machines to either Logstash or Elasticsearch.
Contact us if you would like for us to implement Elast Stack for your oorganization.